For reasons of integrity and trust, all HTTPS Certificates which are issued by Certificate Authorities must be registered into a variety of centralised “transparency logs” – primarily in order to detect “cheating”.
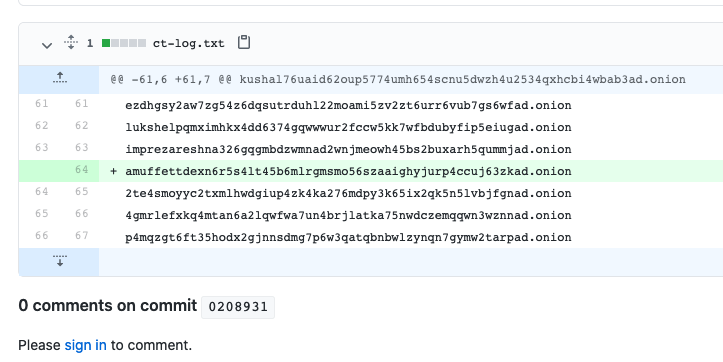
This means that we can see all V3 onions sites which are registered:
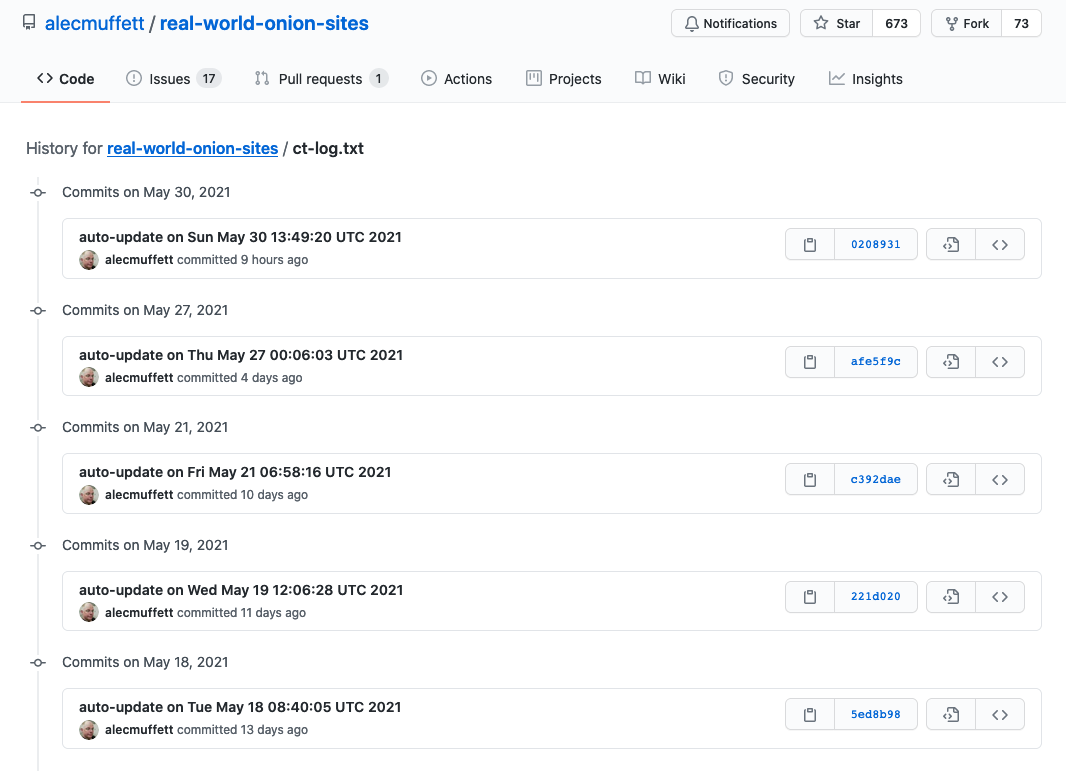
Real World Onion Sites: Certificate Transparency Log
This is both a bad thing and a good thing.
It’s a good (even, great?) thing for awareness, and for publication or announcement of legitimate, real-world onion websites. The certificate transparency logs operate as a directory of extant sites which can be scanned.
The bad thing? It’s a massive cost, and an unnecessary exposure, for people who want to use ephemeral onion addressing for single purposes, e.g. for voice or video calling over WebRTC which will mandate use of HTTPS in most browsers.
The process of “proving” site ownership for certificate issuance may also harm the use of password-protected Onion Addresses.
The solution in this space is/should-be that TorBrowser adopts something like Same Origin Onion Certificates, a narrowly-defined specification for homebrew, signature-irrelevant certificates which will be compatible with current and future web innovations such as HTTP/2 Connection Coalescing and yet not require registration in a log.
Leave a Reply